-
Постов
3 -
Зарегистрирован
-
Посещение
Тип контента
Профили
Форумы
Галерея
Загрузки
Блоги
События
Сообщения, опубликованные Konstantin Rezvykh
-
-
5 минут назад, Sirex сказал:
Здравствуйте. При перезагрузки роутера xkeen не стартует, как можно это исправить?
Модель роутера: kn-1811Cценарий initrc: /opt/etc/init.d/rc.unslung
Выполнял xkeen -ri
start_delay=20
Логи при старте xkeen:~ # xkeen -status
Прокси-клиент не запущен
~ # xkeen -start
Xray 1.8.7 (Xray, Penetrates Everything.) 3f0bc13 (go1.21.5 linux/arm64)
A unified platform for anti-censorship.
2024/01/23 15:07:31 Using confdir from env: /opt/etc/xray/configs
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/01_log.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/02_stats.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/03_dns.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/04_reverse.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/05_fake-dns.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/06_transport.json
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/07_inbounds.json
2024/01/23 15:07:31 [Info] infra/conf: [/opt/etc/xray/configs/07_inbounds.json] prepend outbound with tag: out-russia
2024/01/23 15:07:31 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/08_outbounds.json
2024/01/23 15:07:32 [Info] infra/conf: [/opt/etc/xray/configs/08_outbounds.json] appended inbound with tag: tproxy
2024/01/23 15:07:32 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/09_policy.json
2024/01/23 15:07:32 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/10_routing.json
2024/01/23 15:07:32 [Info] infra/conf/serial: Reading config: /opt/etc/xray/configs/11_fallbacks.json
Прокси-клиент запущен
Проверьте права файла S24xray.
-
Добрый вечер! tproxy заработал (со 127.0.0.1 в конфиге inbounds), для диагностики просили:
Скрытый текст~ # iptables -t mangle -nL PREROUTING -v Chain PREROUTING (policy ACCEPT 6507 packets, 2239K bytes) pkts bytes target prot opt in out source destination 45 6140 _NDM_PREROUTING_MC all -- * * 0.0.0.0/0 224.0.0.0/4 14274 3025K _NDM_IPSEC_PREROUTING all -- * * 0.0.0.0/0 0.0.0.0/0 14274 3025K _NDM_HOTSPOT_PRERT all -- * * 0.0.0.0/0 0.0.0.0/0 8175 833K xkeen all -- * * 0.0.0.0/0 0.0.0.0/0 connmark match 0xffffd00 ! ctstate INVALID ~ # iptables -t mangle -nL xkeen -v Chain xkeen (1 references) pkts bytes target prot opt in out source destination 0 0 RETURN all -- * * 0.0.0.0/0 0.0.0.0/8 0 0 RETURN all -- * * 0.0.0.0/0 10.0.0.0/8 17 1166 RETURN all -- * * 0.0.0.0/0 100.64.0.0/10 0 0 RETURN all -- * * 0.0.0.0/0 127.0.0.0/8 0 0 RETURN all -- * * 0.0.0.0/0 169.254.0.0/16 0 0 RETURN all -- * * 0.0.0.0/0 172.16.0.0/12 0 0 RETURN all -- * * 0.0.0.0/0 192.0.0.0/24 0 0 RETURN all -- * * 0.0.0.0/0 192.0.2.0/24 547 56769 RETURN all -- * * 0.0.0.0/0 192.168.0.0/16 0 0 RETURN all -- * * 0.0.0.0/0 198.18.0.0/15 0 0 RETURN all -- * * 0.0.0.0/0 198.51.100.0/24 0 0 RETURN all -- * * 0.0.0.0/0 203.0.113.0/24 34 4831 RETURN all -- * * 0.0.0.0/0 224.0.0.0/4 0 0 RETURN all -- * * 0.0.0.0/0 240.0.0.0/4 0 0 RETURN all -- * * 0.0.0.0/0 255.255.255.255 7064 665K TPROXY tcp -- * * 0.0.0.0/0 0.0.0.0/0 TPROXY redirect 127.0.0.1:54836 mark 0x111/0xffffffff 1024 158K TPROXY udp -- * * 0.0.0.0/0 0.0.0.0/0 TPROXY redirect 127.0.0.1:54836 mark 0x111/0xffffffff ~ # cat /opt/etc/ndm/netfilter.d/proxy.sh #!/bin/sh mode_proxy="TPROXY" network="tcp udp" name_prerouting_chain="xkeen" name_output_chain="xkeen_mask" name_profile="xkeen" port_proxy="54836" port_donor="" policy_mark="0xffffd00" table_redirect="nat" table_tproxy="mangle" table_mark="0x111" table_id="111" file_dns="" port_dns="53" directory_os_modules=/lib/modules/4.9-ndm-5 directory_user_modules=/opt/lib/modules load_module() { local module=${1} local directory_modules if [ -f "${directory_user_modules}/${module}" ] then directory_modules="${directory_user_modules}" else directory_modules="${directory_os_modules}" fi insmod ${directory_modules}/${module} >/dev/null 2>&1 } if [ "${mode_proxy}" = "REDIRECT" ]; then network="tcp" else network="tcp udp" fi if [ -n "${file_dns}" ]; then port_donor="${port_dns},${port_donor}" fi iptables_supported=$(command -v iptables >/dev/null 2>&1 && echo true || echo false) ip6tables_supported=$(command -v ip6tables >/dev/null 2>&1 && echo true || echo false) add_ipt_rule() { local family="${1}" local table="${2}" local chain="${3}" shift 3 if { [ "${family}" = "iptables" ] && [ "${iptables_supported}" = "false" ]; } || { [ "${family}" = "ip6tables" ] && [ "${ip6tables_supported}" = "false" ]; }; then return fi if ! "${family}" -t "${table}" -nL ${name_prerouting_chain} >/dev/null 2>&1; then "${family}" -t "${table}" -N ${name_prerouting_chain} >/dev/null 2>&1 || exit 0 add_exclude_rules ${name_prerouting_chain} for net in ${network}; do case "${mode_proxy}" in "REDIRECT") "${family}" -t "${table}" -A ${name_prerouting_chain} -p "${net}" -j REDIRECT --to-port "${port_proxy}" >/dev/null 2>&1 ;; "TPROXY") "${family}" -t "${table}" -A ${name_prerouting_chain} -p "${net}" -j TPROXY --on-ip "${proxy_ip}" --on-port "${port_proxy}" --tproxy-mark "${table_mark}" >/dev/null 2>&1 ;; *) exit 0 ;; esac done fi if [ -n "${file_dns}" ]; then if ! "${family}" -t "${table}" -nL ${name_output_chain} >/dev/null 2>&1; then "${family}" -t "${table}" -N ${name_output_chain} >/dev/null 2>&1 || exit 0 add_exclude_rules ${name_output_chain} "${family}" -t "${table}" -A ${name_output_chain} -j CONNMARK --set-mark "${table_mark}" fi fi } add_exclude_rules() { local chain="${1}" for exclude in ${exclude_list}; do if ([ "${exclude}" = "192.168.0.0/16" ] || [ "${exclude}" = "fd00::/8" ]) && [ -n "${file_dns}" ]; then "${family}" -t "${table}" -A ${chain} -d "${exclude}" -p tcp ! --dport 53 -j RETURN 2>/dev/null "${family}" -t "${table}" -A ${chain} -d "${exclude}" -p udp ! --dport 53 -j RETURN 2>/dev/null else "${family}" -t "${table}" -A ${chain} -d "${exclude}" -j RETURN 2>/dev/null fi done } configure_route() { local ip_version="${1}" if ! ip -"${ip_version}" rule show | grep -q "fwmark ${table_mark} lookup ${table_id}" >/dev/null 2>&1; then ip -"${ip_version}" rule add fwmark "${table_mark}" lookup "${table_id}" >/dev/null 2>&1 ip -"${ip_version}" route add local default dev lo table "${table_id}" >/dev/null 2>&1 fi } case "${mode_proxy}" in "TPROXY") active_table="${table_tproxy}" load_module xt_TPROXY.ko ;; "REDIRECT") active_table="${table_redirect}" ;; *) exit 0 ;; esac for family in iptables ip6tables; do if [ "${family}" = "ip6tables" ]; then exclude_list="0000::/8 0100::/64 0200::/7 2001:0002::/48 2001:0010::/28 2001:0db8::/32 2002::/16 3ffe::/16 fc00::/7 fd00::/8 fe80::/10 fec0::/10 ff00::/8 ::1/128 ::ffff:0:0/96 64:ff9b::/96 64:ff9b:1::/48 100::/64 2001::/23" proxy_ip="::1" configure_route 6 else exclude_list="0.0.0.0/8 10.0.0.0/8 100.64.0.0/10 127.0.0.0/8 169.254.0.0/16 172.16.0.0/12 192.0.0.0/24 192.0.2.0/24 192.168.0.0/16 198.18.0.0/15 198.51.100.0/24 203.0.113.0/24 224.0.0.0/4 240.0.0.0/4 255.255.255.255/32" proxy_ip="127.0.0.1" configure_route 4 fi add_ipt_rule "${family}" "${active_table}" "${name_prerouting_chain}" if [ -n "${file_dns}" ]; then add_ipt_rule "${family}" "${active_table}" "${name_output_chain}" fi done if [ -n "${port_donor}" ]; then load_module xt_multiport.ko load_module xt_owner.ko for net in ${network}; do for family in iptables ip6tables; do if [ "${family}" = "iptables" ] && { ! iptables -t "${active_table}" -C PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -p "${net}" -m multiport --dports "${port_donor}" -j ${name_prerouting_chain} >/dev/null 2>&1; }; then iptables -t "${active_table}" -A PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -p "${net}" -m multiport --dports "${port_donor}" -j ${name_prerouting_chain} >/dev/null 2>&1 fi if [ "${family}" = "ip6tables" ] && { ! ip6tables -t "${active_table}" -C PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -p "${net}" -m multiport --dports "${port_donor}" -j ${name_prerouting_chain} >/dev/null 2>&1; }; then ip6tables -t "${active_table}" -A PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -p "${net}" -m multiport --dports "${port_donor}" -j ${name_prerouting_chain} >/dev/null 2>&1 fi if [ -n "${file_dns}" ]; then if [ "${family}" = "iptables" ] && { ! iptables -t "${active_table}" -C OUTPUT -m owner ! --gid-owner ${name_profile} -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1; }; then iptables -t "${active_table}" -A OUTPUT -m owner ! --gid-owner ${name_profile} -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1 fi if [ "${family}" = "ip6tables" ] && { ! ip6tables -t "${active_table}" -C OUTPUT -m owner ! --gid-owner ${name_profile} -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1; }; then ip6tables -t "${active_table}" -A OUTPUT -m owner ! --gid-owner ${name_profile} -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1 fi fi done done else for family in iptables ip6tables; do if [ "${family}" = "iptables" ] && { ! iptables -t "${active_table}" -C PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -j ${name_prerouting_chain} >/dev/null 2>&1; }; then iptables -t "${active_table}" -A PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -j ${name_prerouting_chain} >/dev/null 2>&1 fi if [ "${family}" = "ip6tables" ] && { ! ip6tables -t "${active_table}" -C PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -j ${name_prerouting_chain} >/dev/null 2>&1; }; then ip6tables -t "${active_table}" -A PREROUTING -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID -j ${name_prerouting_chain} >/dev/null 2>&1 fi if [ -n "${file_dns}" ]; then if [ "${family}" = "iptables" ] && { ! iptables -t "${active_table}" -C OUTPUT -m owner ! --gid-owner ${name_profile} -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1; }; then iptables -t "${active_table}" -A OUTPUT -m owner ! --gid-owner ${name_profile} -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1 fi if [ "${family}" = "ip6tables" ] && { ! ip6tables -t "${active_table}" -C OUTPUT -m owner ! --gid-owner ${name_profile} -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1; }; then ip6tables -t "${active_table}" -A OUTPUT -m owner ! --gid-owner ${name_profile} -m connmark --mark "${policy_mark}" -m conntrack ! --ctstate INVALID ! -p icmp -j ${name_output_chain} >/dev/null 2>&1 fi fi done fi exit 0-
 2
2
-


Xkeen
в Каталог готовых решений Opkg
Опубликовано
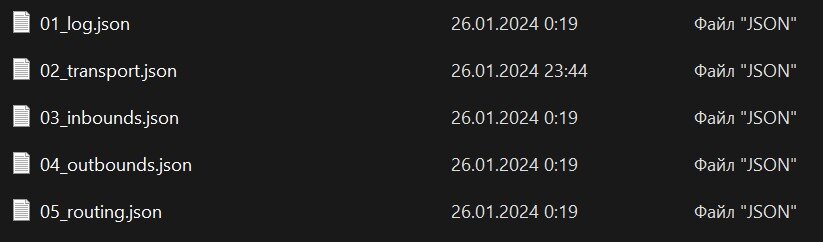
После сегодняшних обновлений все сломалось, пришлось поставить все заново. Нормально, что сейчас всего 5 файлов конфига и их номера поменялись? Как то это пропустил в чейнджлогах.